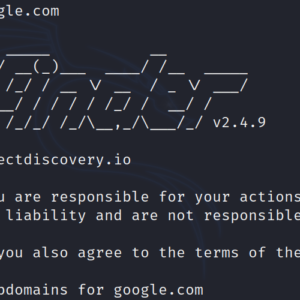
Subfinder: Subdomain enumeration tool Hello Friends, in this blog we are going to learn about the subdomain enumeration tool subfinder…
Reconnaissance ctf – tryhackme Hello Friends! I’m going to make a write-up about the secuneus CTF room Task 3 Reconnaissance…
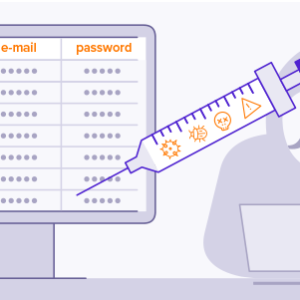
Secuneus CTF SqlI-Tryhackme Hello Friends, I’m going to make a write-up about tryhackme’s room task 6 Secuneus CTF SQLi In…
News: 4 more fall prey to cyber scams in Chandigarh The cyber cell of Chandigarh Police have received four more…
News: Hacker reports vulnerability and possible data leak in Vodafone Idea’s subscriber database portal Database portal comprises information of all…
News: China Cyber Attack On Power Grid Near Ladakh Between Aug-March: Report New Delhi: Chinese state-sponsored hackers targeted Indian electricity…
News: How ‘Chinese app scams’ have been targeting lakhs of Indians, looting crores since WFH took off New Delhi: The 27-year-old…
News: Trezor cryptocurrency wallets targeted with phishing attacks following Mailchimp compromise Cryptocurrency hardware wallet owners are being targeted by a phishing scam…
News: Delhi Police busts Chinese loan app fraud, 8 held The Intelligence Fusion and Strategic Operations (IFSO) Unit of Delhi…
News: Cyber Crime losses rise to 63 crore in fy20-21: Govt. New Delhi: The extent of loss due to cyber…
News: Lapsus$ hacking group: Seven, including 16-year-old from Oxford, arrested in UK Seven teenagers have been arrested by the London…
News: Data centres in India faced 51 million cyber attacks in 9 months The data centres in India captured more than 51…
News: Bengaluru: Nimhans sees ransomware attack; IT cell checks spread BENGALURU: Premier mental health institute Nimhans faced a cybersecurity threat…
News: Beware! Cyber scammers using AAP’s Rs 1,000 poll promise to defraud Punjab women As the Aam Aadmi Party (AAP)…
News: Honda Bug Let Attackers Unlock and Start the Car Honda and Acura have recently been found to have a…
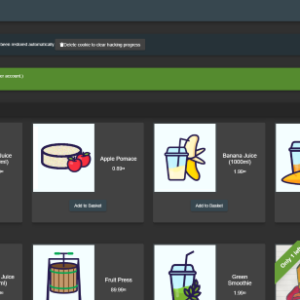
Owasp Juicy Shop | Sensitive Data Exposure Sensitive Data Exposure: Sensitive Data Exposure vulnerabilities can occur when a web application…
News: India among top 10 victims of ransomware attacks; Maharashtra the most affected Having perfected their malware, the cybercriminals developed…
News: Power transmission: Punjab among 8 states targeted by Chinese hackers in past month From last week of February to…
Owasp Juicy shop | Broken Authentication In this blog we are going to learn about the broken authentication vulnerability Owasp…
News: Nation-State Cyber-Attack Tools Enter Black Market, With Rise In Ransomware As A Service Cyber-attacks are on the rise globally,…